
Penetration testing is a structured cyber security practice where ethical hackers simulate real-world attacks to identify vulnerabilities in systems, networks, and web applications. Rather than waiting for a breach to occur, organisations rely on a penetration test (pen test) to proactively uncover and fix security weaknesses before they can be exploited.
Penetration testing plays a critical role in modern cybersecurity strategies, helping businesses understand how attackers think and where defences may fail. From web application penetration testing to external network testing, it provides practical insight into real risks that could impact sensitive data and operations.
What is penetration testing in cyber security and how does a pen test work?
A penetration test (pen test) is a simulated hacking attempt performed by cybersecurity professionals to identify and exploit vulnerabilities in a controlled environment. It replicates how a real attacker would attempt to gain access, move through systems, and extract sensitive information.
Unlike automated vulnerability scanning, penetration testing combines tools and human expertise to uncover deeper security vulnerabilities. This approach helps organisations understand actual risk exposure rather than just theoretical weaknesses.
Why penetration testing is important for cyber security
Penetration testing helps organisations detect and address vulnerabilities before they are exploited in real cyber attacks. According to IBM’s 2025 Cost of a Data Breach Report, the global average cost of a data breach was USD 4.44 million, highlighting the financial impact of security incidents and the value of proactive testing. It also helps reduce the likelihood and impact of breaches by identifying weaknesses before attackers exploit them.
Penetration testing also helps organisations identify both known and unknown vulnerabilities while simulating real-world attack scenarios. It validates existing security controls such as firewalls and access management systems, while supporting compliance requirements for standards like PCI DSS, which require testing both annually and after significant system changes.
How penetration testing supports compliance requirements
Penetration testing also plays a key role in meeting compliance standards. Frameworks such as PCI DSS require penetration testing at least annually and after significant changes to the cardholder data environment. Under PCI DSS, testing must cover the cardholder data environment, including relevant internal and external attack surfaces, and should also validate segmentation controls where applicable.
Many Australian organisations conduct penetration testing regularly to align with compliance frameworks such as PCI DSS and APRA CPS 234, particularly in sectors handling sensitive financial or customer data. For APRA-regulated entities, CPS 234 requires a systematic testing program for information security controls, with the nature and frequency of testing commensurate with the rate of change in threats, the criticality and sensitivity of the information asset, the consequences of an information security incident, and the materiality and frequency of change to information assets.
APRA also expects entities to review the sufficiency of the testing program at least annually or when there is a material change to information assets or the business environment.
Who performs penetration testing and what skills do they need?
Penetration tests are carried out by ethical hackers, also known as penetration testers or cybersecurity experts. These specialists use the same tools and techniques as malicious attackers but operate within legal and controlled boundaries.
Internal teams vs external penetration testing providers
Organisations often rely on both internal security teams and external penetration testing providers to strengthen their cybersecurity approach. Internal teams provide system familiarity and continuous testing, helping monitor and address vulnerabilities over time. External penetration testing providers bring independent validation and specialised expertise across a range of environments.
Together, these approaches create a more balanced and effective security strategy.
What are the different types of penetration testing in cyber security?
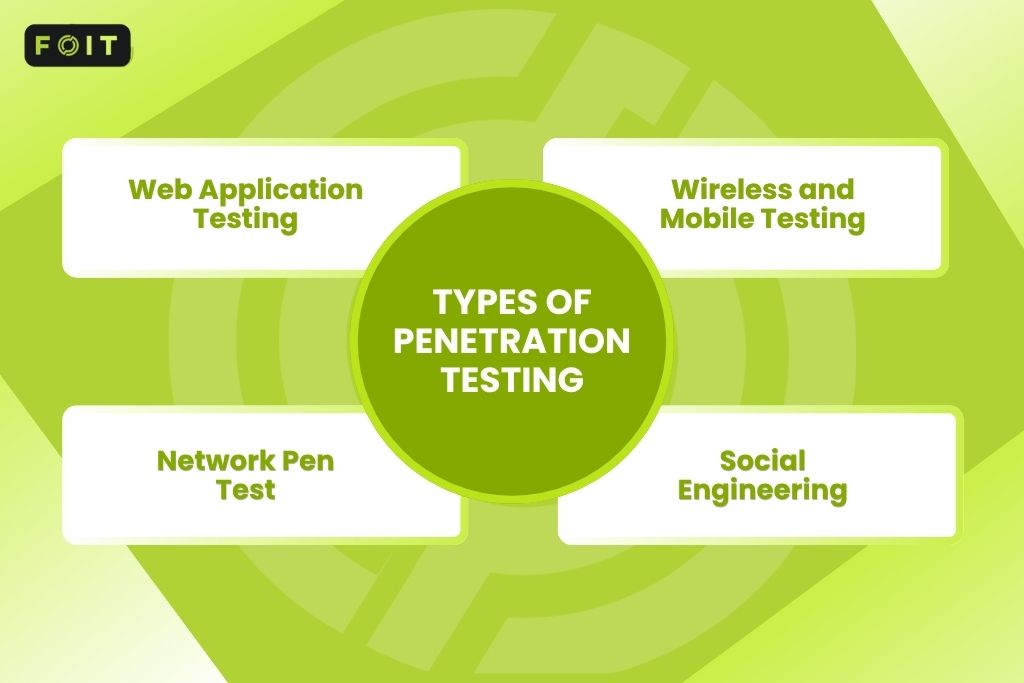
Different types of penetration testing focus on specific systems and attack surfaces to uncover vulnerabilities effectively. Common examples include web application testing, network testing, wireless testing, mobile testing, and social engineering assessments, depending on the organisation’s risks and scope.
Web application penetration testing
This type targets vulnerabilities in web applications, including SQL injection, authentication flaws, and insecure APIs. It ensures that applications handling sensitive data remain secure.
Wireless and mobile penetration testing
This identifies vulnerabilities in wireless networks and mobile devices, ensuring secure connectivity and remote access.
Network penetration testing
Network penetration testing evaluates both internal and external infrastructure to identify potential security gaps. Internal penetration testing simulates insider threats, focusing on risks within the organization’s network. External penetration testing targets internet-facing systems to detect vulnerabilities exposed to outside attackers.
Social engineering penetration testing
This method focuses on human vulnerabilities through techniques such as phishing and impersonation, testing how employees respond to manipulation attempts.
What is the penetration testing process step by step?
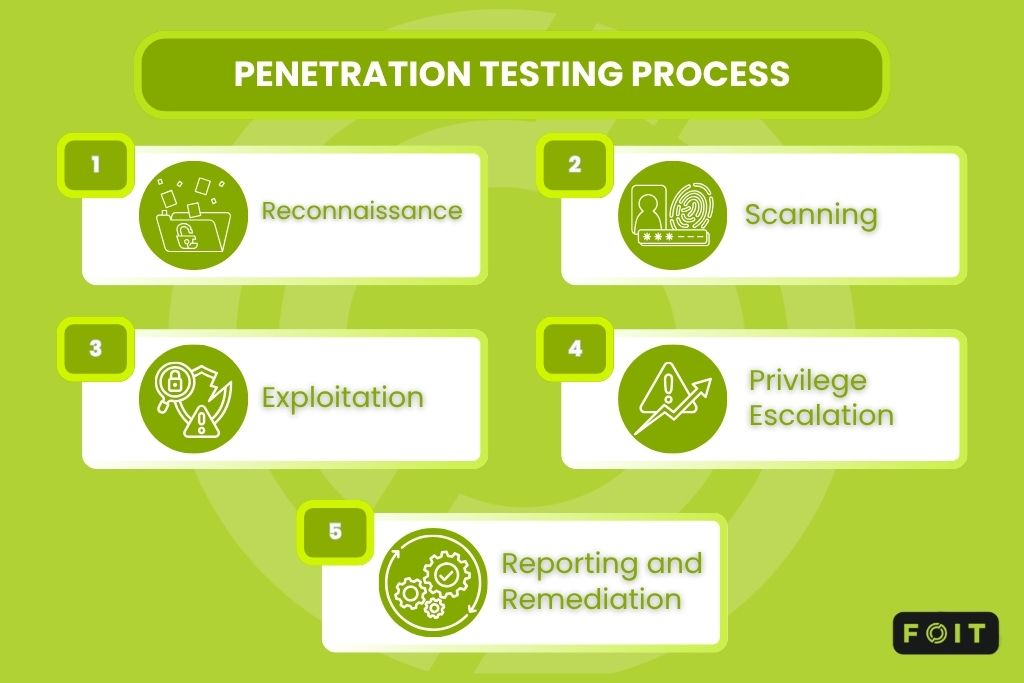
The penetration testing process follows a structured methodology designed to simulate real cyber attacks and identify vulnerabilities effectively. A typical workflow includes reconnaissance, scanning and enumeration, exploitation, post-exploitation activities such as privilege escalation or lateral movement where permitted, and final reporting with remediation guidance.
1. Reconnaissance
Penetration testers gather information about the target system, including domains, IP addresses, and infrastructure.
2. Scanning and vulnerability assessment
Tools and manual techniques are used to identify potential entry points and security weaknesses.
3. Exploitation
Testers attempt to exploit vulnerabilities and gain access to systems or sensitive data.
4. Privilege escalation and lateral movement
Once access is gained, testers simulate how attackers expand control across the network.
5. Reporting and remediation
Findings are documented in a pentest report, including severity levels and recommended fixes.
What are penetration test rules of engagement and why do they matter?
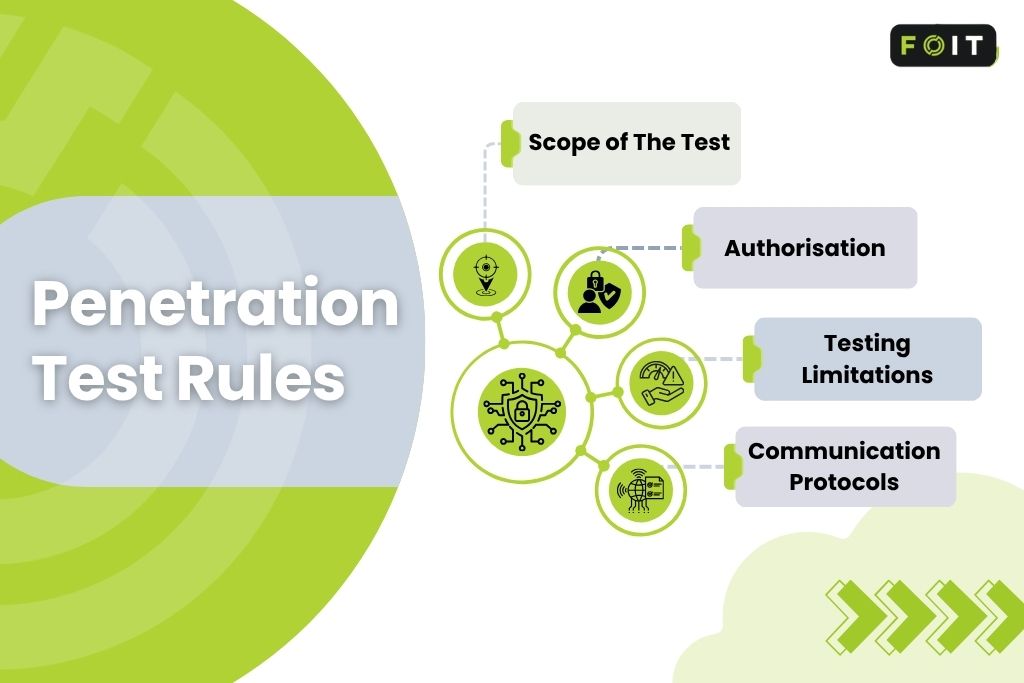
Penetration test rules of engagement define the boundaries, permissions, and expectations for a penetration test. They ensure testing is conducted safely, ethically, and without disrupting business operations.
Scope of the test
Defines which systems, applications, and networks are included or excluded.
Authorisation and permissions
Explicit written approval is required before any testing begins.
Testing limitations
Specifies allowed tools and techniques to avoid operational risks.
Communication protocols
Ensures critical vulnerabilities are reported immediately to the security team.
How to read a pentest report example and understand results
A pentest report translates technical findings into clear, actionable insights that help both technical and non-technical stakeholders understand security risks. A well-structured report usually includes an executive summary, detailed findings, affected systems, severity ratings, evidence, and remediation recommendations.
Pentest report structure explained
A typical pentest report includes an executive summary outlining the organisation’s security posture, followed by detailed findings with severity levels, evidence of exploitation, and affected systems. It also includes remediation recommendations, helping security teams understand how to fix vulnerabilities and reduce risk effectively.
How to prioritise vulnerabilities
Vulnerabilities should be prioritised based on their risk level and potential impact on sensitive data or business operations. Critical issues that allow unauthorised access or data exposure must be addressed first, followed by high-risk vulnerabilities, while medium and low-risk issues can be resolved based on operational priorities.
Why invest in penetration testing and what is the ROI?
Penetration testing delivers measurable value by reducing the likelihood and impact of cyber incidents. By identifying vulnerabilities before they are exploited, organisations can avoid costly breaches, minimise downtime, and strengthen their overall cyber security posture.
Key ROI benefits of a penetration test
Investing in a penetration test helps organisations prevent financial losses linked to data breaches and operational disruptions, while also reducing the risk of regulatory penalties. It also improves customer trust by demonstrating a proactive approach to data protection, while supporting long-term cyber security strategy through continuous risk visibility and improvement.
How much does penetration testing cost in Australia?
Penetration testing costs in Australia depend on scope, complexity, reporting requirements, and the number of systems being tested. The following pricing ranges are indicative only. Actual quotes vary based on scope, asset count, environment complexity, testing depth, compliance requirements, and whether retesting is included.
How often should penetration testing be conducted?
Penetration testing should be conducted regularly to maintain a strong and up-to-date security posture, particularly as cyber threats continue to evolve. While annual testing is a common baseline for many organisations, it may not be sufficient for high-risk environments or rapidly changing systems. In practice, testing frequency should reflect risk, regulatory obligations, and the pace of infrastructure or application change, with additional testing after significant updates or major security changes.
Recommended penetration testing frequency
Most organisations should conduct penetration testing at least once per year to align with compliance requirements such as PCI DSS. However, more frequent testing, including quarterly assessments, is recommended for high-risk industries or organisations handling sensitive data, as well as after major system updates, infrastructure changes, or new application deployments.
What penetration testing tools do ethical hackers use?
Penetration testers use a combination of specialised tools and manual techniques to simulate real-world cyber attacks and identify vulnerabilities. While tools help automate scanning and analysis, human expertise is essential to interpret results and replicate realistic attack scenarios.
Common penetration testing tools
Some of the most widely used penetration testing tools include Metasploit for exploitation, Nmap for network scanning, Burp Suite for web application testing, and Wireshark for network analysis. These tools help identify entry points, analyse traffic, and test system defences across different environments.
Why tools alone are not enough in a pen test
Tools can detect vulnerabilities, but they cannot fully replicate the behaviour of a skilled attacker. Human-led testing is critical for chaining vulnerabilities together, simulating complex attack paths, and uncovering deeper security risks that automated tools may overlook.
How to choose the right penetration testing provider
Choosing the right penetration testing provider is essential for obtaining accurate results and driving meaningful improvements in cyber security. A reliable provider not only identifies vulnerabilities but also delivers clear insights that help organisations strengthen their overall security posture.
What to look for in a penetration testing provider
A strong penetration testing provider should demonstrate proven experience in cybersecurity and ethical hacking, supported by recognised certifications such as OSCP (Offensive Security Certified Professional) or CREST (Council of Registered Ethical Security Testers). They should also offer clear, actionable reporting and use transparent testing methodologies that align with industry standards and business requirements.
Common mistakes to avoid when hiring
Organisations should avoid selecting a provider based solely on cost, as this can lead to incomplete or low-quality assessments. It is better to compare scope, methodology, tester credentials, reporting depth, and retesting support so the engagement produces usable remediation guidance.
Why penetration testing is essential for long term cyber security
Penetration testing provides a practical way to understand how real attackers approach systems and where vulnerabilities are most likely to exist. From our experience at FOIT, the insights gained from a well-executed penetration test often highlight not just technical issues, but also gaps in processes and day-to-day security practices. Penetration testing is most valuable when treated as part of an ongoing security improvement cycle rather than a one-off compliance exercise.
We have seen that when penetration testing is treated as an ongoing process rather than a one-off activity, it becomes significantly more valuable. It allows organisations to continuously refine their cyber security posture, respond to evolving threats, and make informed decisions to protect sensitive information over time.
Frequently asked questions
How long does a penetration test usually take?
A penetration test typically takes between a few days and several weeks, depending on the scope and complexity of the systems being tested. Smaller web application tests may be completed quickly, while enterprise environments require more time. The duration also depends on how deeply testers simulate real-world attack scenarios.
Can penetration testing disrupt business operations?
Penetration testing can impact systems if not properly planned, but it is usually designed to minimise disruption. Most tests follow strict rules of engagement to avoid downtime or data loss. In practice, organisations schedule testing during low-traffic periods to reduce operational risk and ensure business continuity.
Is penetration testing required by Australian regulations?
Penetration testing is not universally mandatory across all Australian organisations, but it is often expected under specific compliance frameworks, industry standards, and contractual obligations. For example, APRA-regulated entities must systematically test security controls under CPS 234, and PCI DSS requires regular penetration testing for in-scope environments.
What is the difference between black box, white box, and grey box testing?
Black box testing simulates an attacker with no internal knowledge of the target. White box testing provides full internal knowledge, such as architecture details, source code, or credentials. Grey box testing falls in between, giving limited information to simulate a realistic but more efficient attack scenario.








